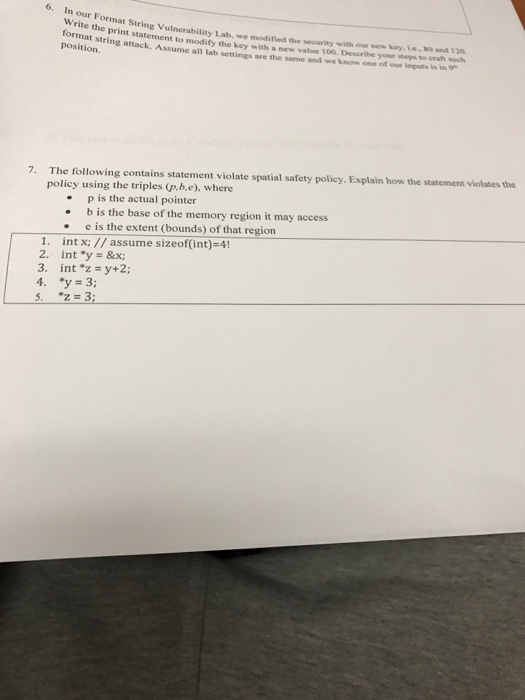
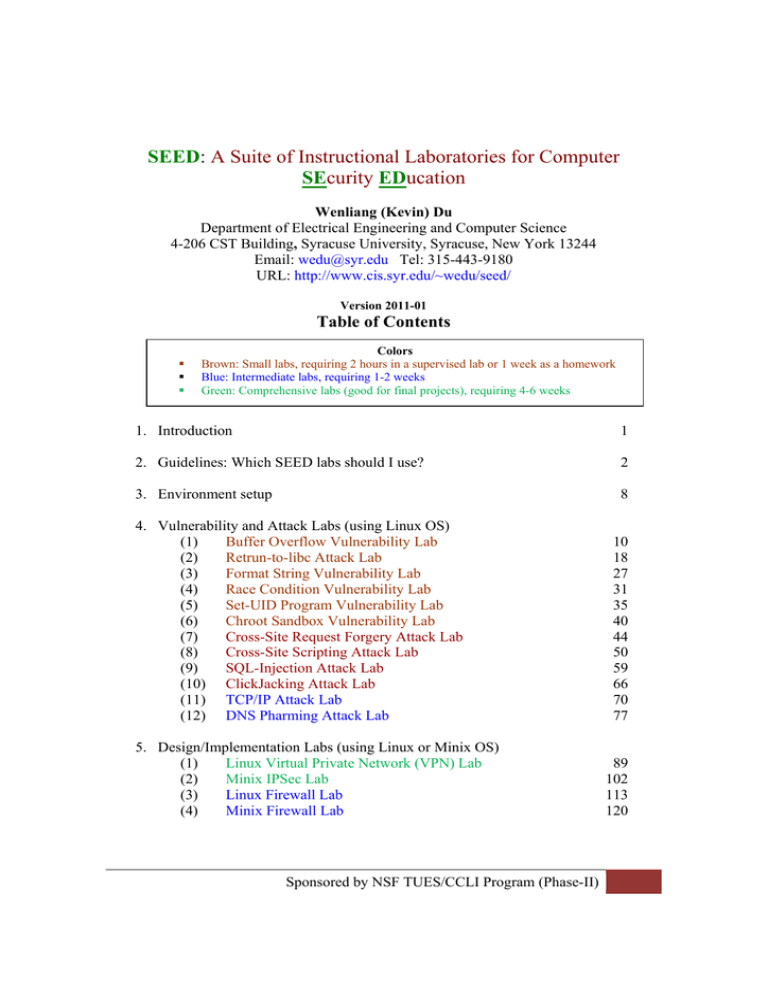
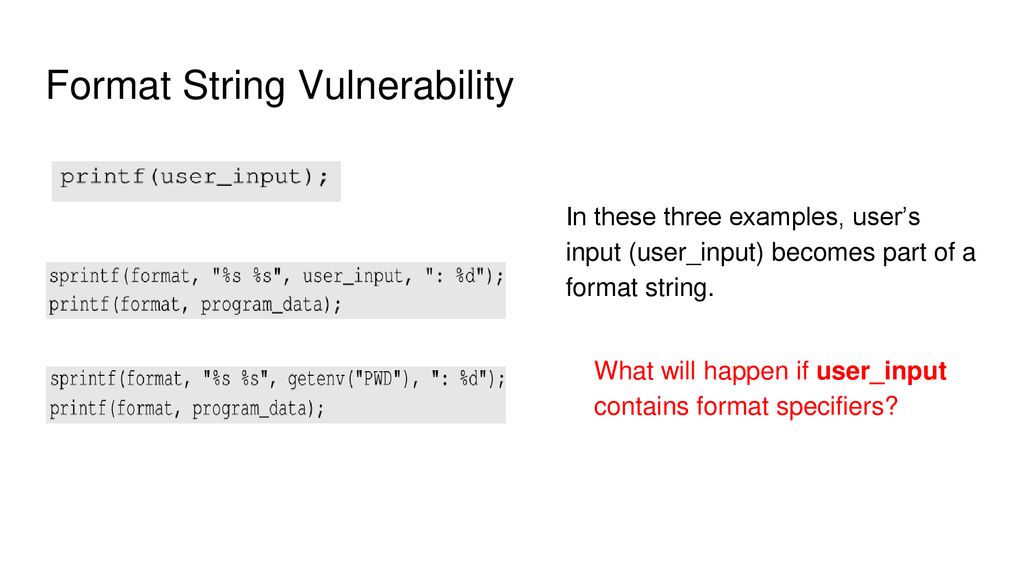
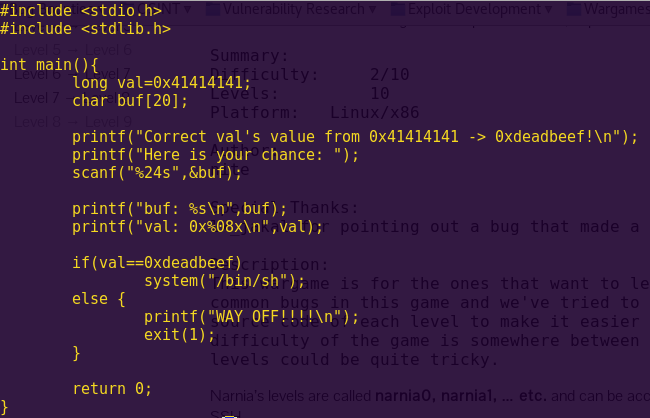
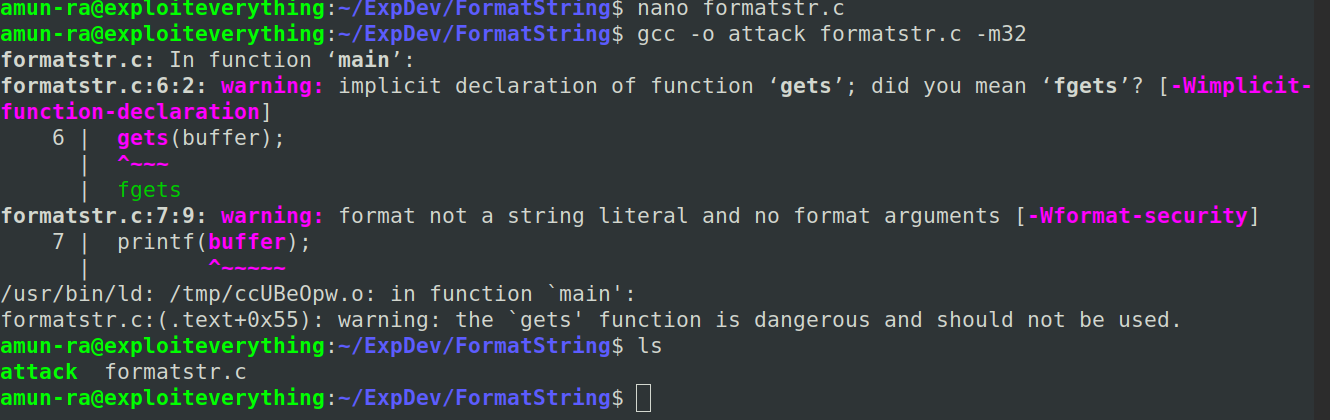
CIS643 - Lab 4.docx - Lab 4: Format String Vulnerability Lab CSE 643: Computer Security Date: February 8, 2022 Abstract: The objective of this lab was | Course Hero

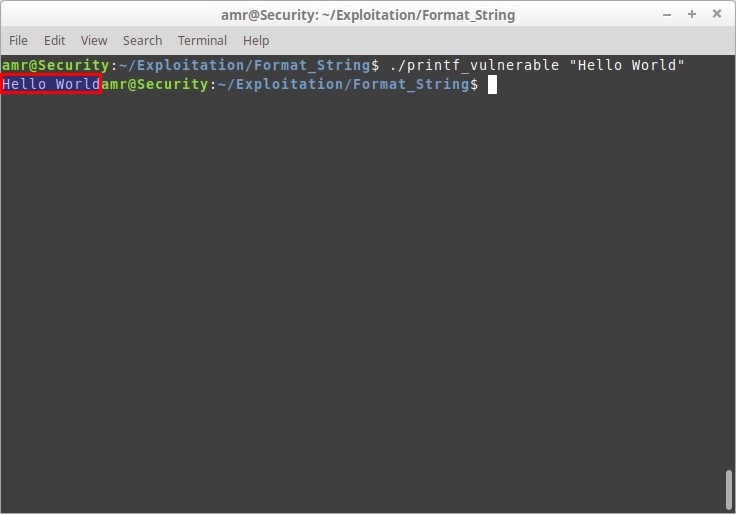
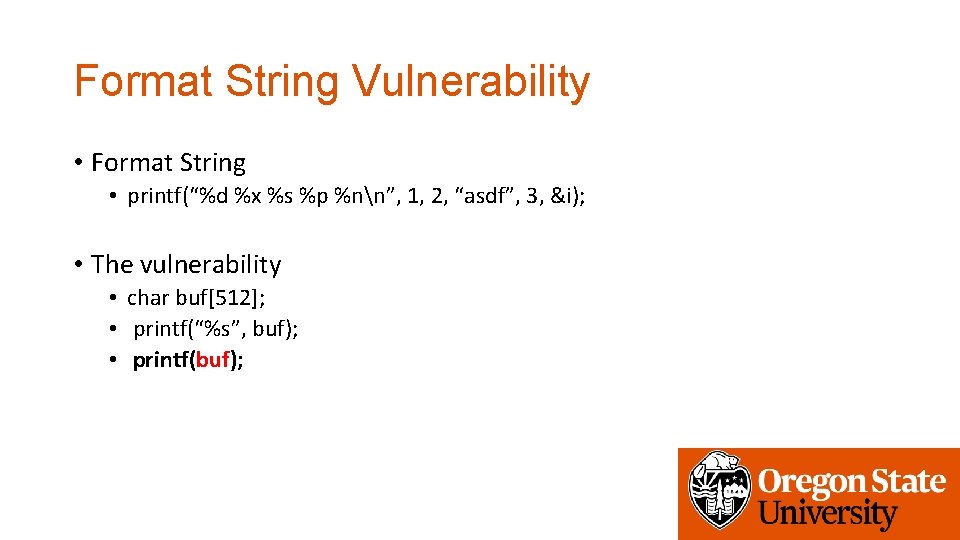
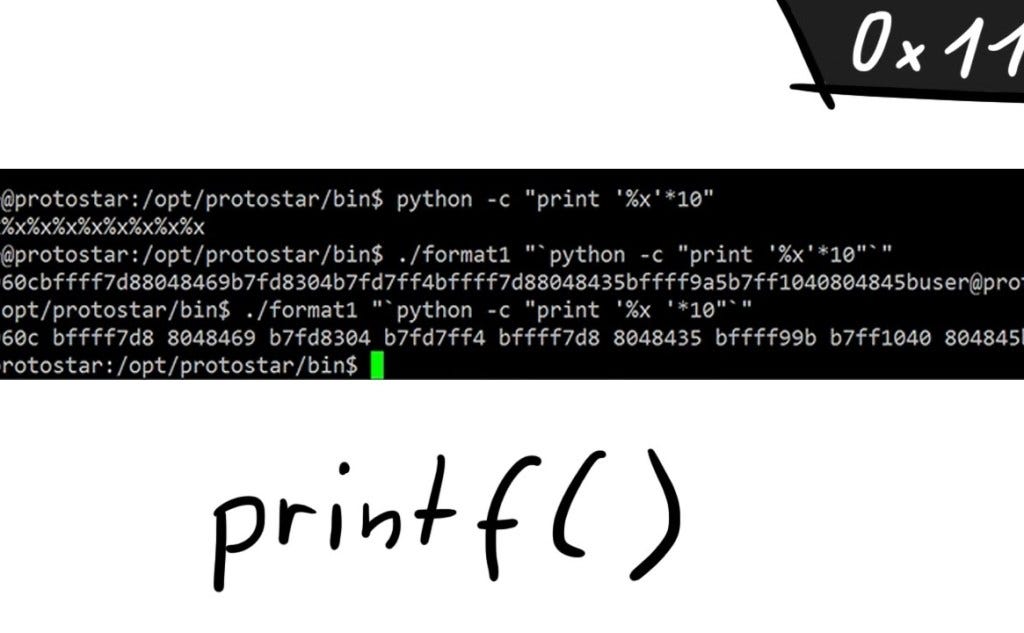
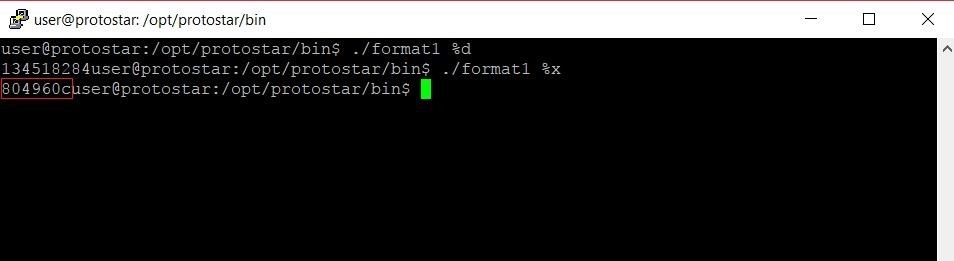
Format String attack .pdf - Format String Vulnerability Lab Task 2: Understanding the Layout of the Stack Firstly, using 1111%n$x ( n is from 1 to 30) | Course Hero


![Lab 07 - Strings [CS Open CourseWare] Lab 07 - Strings [CS Open CourseWare]](https://ocw.cs.pub.ro/courses/_media/cns/labs/info-leak-stack-64.png?w=600&tok=1285d8)